- 1 Post
- 23 Comments

 401·1 month ago
401·1 month agoThe mastodon version of a post or, sadly, tweet.
It’s, uh, not the best name.
But maybe, just maybe, it more appropriately attributes correct value to a social media thing. ;)

 5·2 months ago
5·2 months agoIs there a reason you need a dual book instance instead of a VM or even WINE?
Unless you need direct access to hardware and if you have enough RAM, you can probably avoid dual booting altogether.

 583·4 months ago
583·4 months agoPros:
- you run a home lab
Cons:
- you run a home lab

 2·5 months ago
2·5 months agopfBlockerNG at the network edge and ublockorigin on devices.

 15·7 months ago
15·7 months agoHard to tell from first glance but my guess would be this is fallout from the ongoing
xzdrama. Here: https://www.openwall.com/lists/oss-security/2024/03/29/4
I’m on iOS and do the same thing.
The WireGuard app has a setting to “connect on demand”. It’s in the individual connections/configurations.
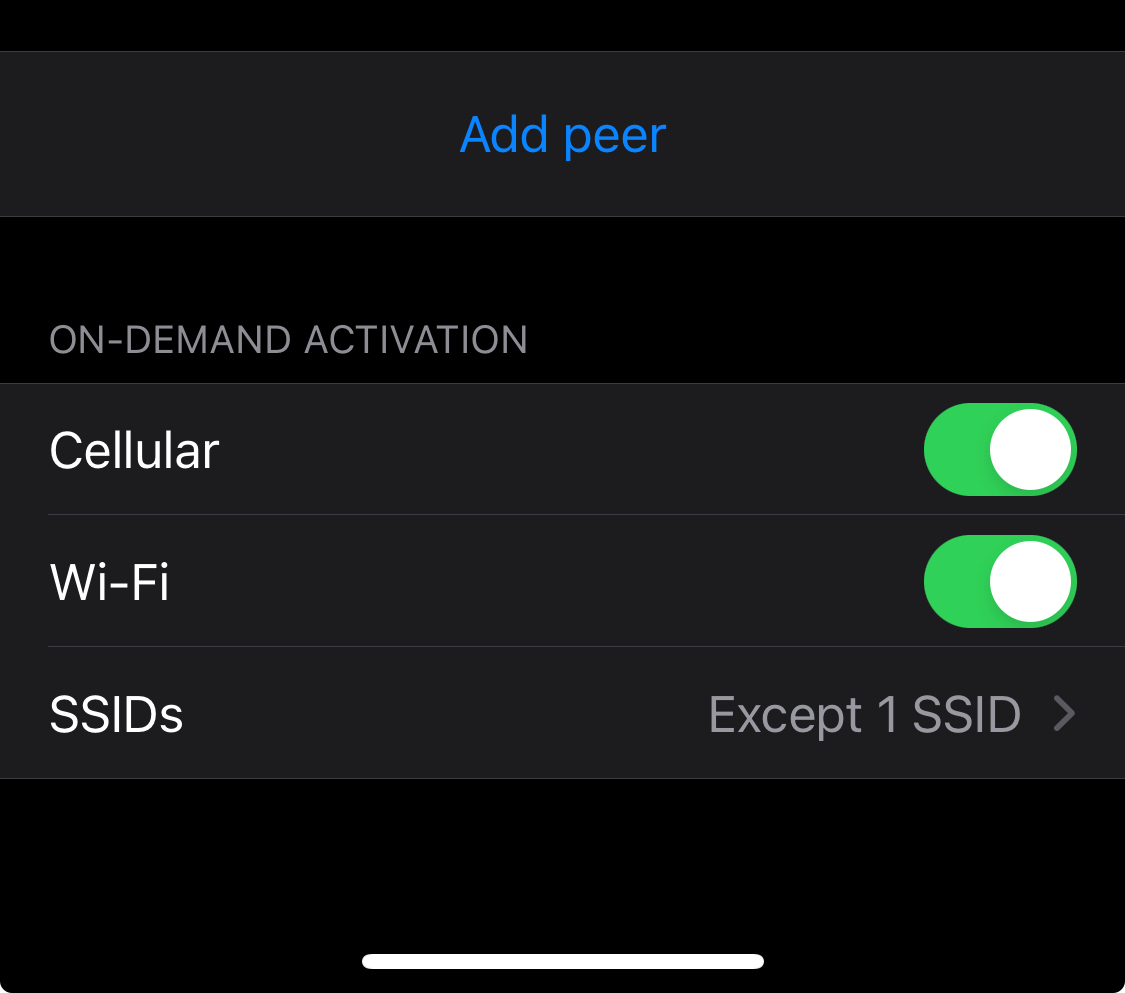
You can then set either included or excluded SSIDs. There’s also an option to always connect when you’re on mobile/cellular data.
I imagine the Android app is similar.

 1·9 months ago
1·9 months agoDM’ed you the link.
Reason: personal GitHub account.

 6·9 months ago
6·9 months agoReddit was aggressively rate limiting tools used to delete and edit content in a funny way when the API pricing was announced. The API wouldn’t return an error, the rate limiting was silent, and the tools would report successful deletion or edits even when the edit or deletion wasn’t made.
I had to modify an existing script to handle the 5-second rate limit and, lieu of deleting, I just rewrote each comment with a farewell.
Even then I did 3 passes (minor additional edits) in cases Reddit was saving previous edits.
My content has stayed edited.

 1·10 months ago
1·10 months agoNeat, I’ll have to look it up. Thanks for sharing!

 101·10 months ago
101·10 months agoNextcloud isn’t exposed, only a WireGuard connection allows for remote access to Nextcloud on my network.
The whole family has WireGuard on their laptops and phones.
They love it, because using WireGuard also means they get a by-default ad-free/tracker-free browsing experience.
Yes, this means I can’t share files securely with outsiders. It’s not a huge problem.

 56·11 months ago
56·11 months agoYou’re conferring a level of agency where none exists.
It appears to “understand.” It appears to be “knowledgeable. “
But LLMs do neither of those things.
Take this note from an OpenAI dev:

It’s that these models have leveraged so much data they’ve been able to map out relationships between words (or images) in way as to be able to generate what seem like new versions of those things.
I grant you that an LLM has more base level knowledge than any one human, but again this is thanks to terrifyingly large dataset and a design that means it can access this data reasonably reliably.
But it is still a prediction model. It just has more context, better design and (most importantly) data to make predictions at a level never before seen.
If you’ve ever had a chance to play with a model at level where you can control some of its basic parameters it offers a glimpse into just how much of a prediction machine it can be.
My favourite game for a while was to give midjourney a wildly vague prompt but crank the chaos up to 100 (literally the chaos flag at the highest level) to see what kind of wild connections exist but are being filtered out during “normal” use.
The same with the GPT-3.5 API in the “early days” - you could return multiple versions of the response and see the sausage being made to a very small degree.
It doesn’t take away from the sense of magic using these tools. It just helps frame what’s going on under the hood.

 4·1 year ago
4·1 year agoIn many cases a lot of sites don’t make it clear that they have a conflict of interest.
You want to push a product on me and you’ll get a cut? Cool, but disclose that.

 4·1 year ago
4·1 year agoUpdate: I went and had a look and there’s a Terraform provider for OPNSense under active development - it covers firewall rules, some unbound configuration options and Wireguard, which is definitely more than enough to get started.
I also found a guide on how to replicate pfBlocker’s functionality on OPNSense that isn’t terribly complicated.
So much of my original comment below is less-than-accurate.
OPNSense is for some, like me, not a viable alternative. pfBlockerNG in particular is the killer feature for me that has no equivalent on OPNSense. If it did I’d switch in a heartbeat.
If I have to go without pfBlockerNG, then I’d likely turn to something that had more “configuration as code” options like VyOS.
Still, it’s nice to know that a fork of a fork of m0n0wall can keep the lights on, and do right by users.

 2·1 year ago
2·1 year agoIf you backup your config now, you’d be able to apply the config to CE 2.7.x.
While this would limit you to an x86 type device, you wouldn’t be out of options.
I am an owner of an SG-3100 as well (we don’t use it anymore), but that device was what soured me on Netgate after using pfSense on a DIY router at our office for years…
I continued to use pfSense because of the sunk costs involved (time, experience, knowledge). This is likely the turning point.

 7·1 year ago
7·1 year agoCluster of Pi4 8GBs. Bought pre-pandemic; love the little things.
Nomad, Consul, Gluster, w/ TrueNas-backed NFS for the big files.
They do all sorts of nifty things for us including Nightscout, LanguageTool OSS, monitoring for ubiquiti, Nextdrive, Grafana (which I use for home monitoring - temps/humidity with alerts), Prometheus & Mimir, Postgres, Codeserver.
Basically I use them to schedule dockerized services I want to run or am interested in playing with/learning.
Also I use Rapsberry Pi zero 2 w’s with Shairport-sync (https://github.com/mikebrady/shairport-sync ) as Airplay 2 streaming bridges for audio equipment that isn’t networked or doesn’t support AirPlay 2.
I’m not sure I’d buy a Pi4 today; but they’ve been great so far.

 9·1 year ago
9·1 year agoDiscomfort can be a good thing; change is often uncomfortable.
But that’s a far cry from being tortured and it sounds like that’s what Musk does to the people around him; using platitudes and words of wisdom as weapons of control and coercion.
As someone who runs a self-hosted mail service (for a few select clients) in AWS, this comment ring true in every way.
One thing that saved us beyond SPF and DKIM was DMARC DNS records and tooling for diagnosing deliverability issues. The tooling isn’t cheap however.
But even then, Microsoft will often blacklist huge ranges of Amazon EIPs and if you’re caught within the scope of that range it’s a slow process to fix.
Also, IP warming is a thing. You need to start slow and at the same time have relatively consistent traffic levels.
Is it worth it, not really no - and I don’t think I’d ever do it again.

 8·1 year ago
8·1 year agoThey do indeed: https://httptoolkit.com/blog/apple-private-access-tokens-attestation/
From the article:
The focus here is primarily on removing captchas, and as such it’s been integrated into Cloudflare (discussed here) and Fastly (here) as a mechanism for recognizing ‘real’ clients without needing other captcha mechanisms.
Fundamentally though, it’s exactly the same concept: a way that web servers can demand your device prove it is a sufficiently ‘legitimate’ device before browsing the web.


Found the other NixOS user. ;)